A GitHub Action to add security scanning of your Kubernetes cluster as part of your pipeline workflow. To customize the scan Create Alcide Advisor Account.
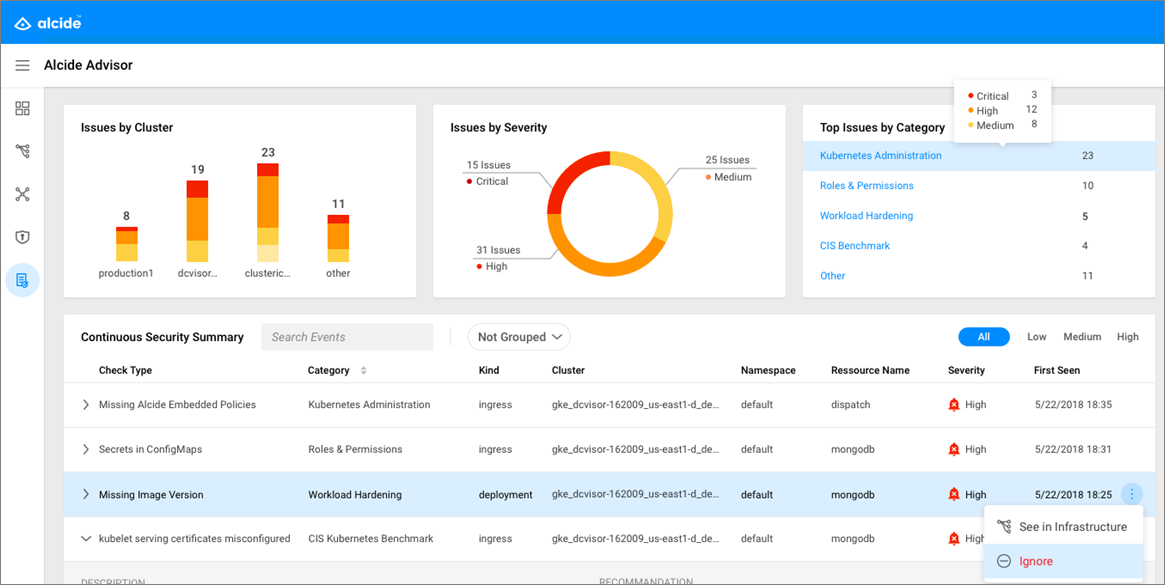
Alcide Advisor is an agentless service for Kubernetes audit and compliance that’s built to ensure a frictionless and secured DevSecOps workflow by layering a hygiene scan of Kubernetes cluster & workloads early in the development process and before moving to production. With Alcide Advisor, you can cover the following security checks:
- Kubernetes infrastructure vulnerability scanning.
- Hunting misplaced secrets, or excessive priviliges for secret access.
- Workload hardening from Pod Security to network policies.
- Istio security configuration and best practices.
- Ingress Controllers for security best practices.
- Kubernetes API server access privileges.
- Kubernetes operators security best practices.
- Deployment conformance to labeling, annotating, resource limits and much more ...
Create a workflow YAML file in your .github/workflows directory. An example workflow is available below.
For more information, reference the GitHub Help Documentation for Creating a workflow file.
For more information on inputs, see the API Documentation
include_namespaces: Namespaces to include in the scan - defaults to allexclude_namespaces: Namespaces to exclude in the scan - defaults to kube-system,istio-systemoutput_file: Scan result file name. You can publish this artifact in a later step.fail_on_critical: Fail the task if critical findings observed.policy_profile:Alcide policy profile the cluster will be scanned against.policy_profile_id: The profile id with which cluster should be scanned. Note - Alcide Api Key is required to run a scan with customized profilealcide_apikey: Alcide API Key - to run advisor scan with customized profile an api-key is needed - login to your account to obtain onealcide_apiserver: Alcide API Server - The api server provisioned to your account
Create a workflow (eg: .github/workflows/advisor-scan.yml):
name: Alcide Advisor Workflow Example
on:
pull_request:
push:
branches:
- '*'
- '!master'
jobs:
advisor-test:
runs-on: ubuntu-latest
steps:
- name: Checkout
uses: actions/checkout@v1
- name: Launch Cluster
uses: helm/kind-action@v1.0.0-alpha.3
with:
version: v0.7.0
name: kruzer
node_image: kindest/node:v1.16.4
wait: 5m
install_local_path_provisioner: true
- name: Test
run: |
kubectl cluster-info
kubectl get storageclass standard
- name: Scan Local Cluster
uses: alcideio/advisor-action@v1.1.0
with:
exclude_namespaces: '-'
include_namespaces: '*'
output_file: 'advisor-scan.html'
- name: Upload Alcide Advisor Scan Report
uses: actions/upload-artifact@v1
with:
name: advisor-scan.html
path: advisor-scan.html This uses @alcideio/advisor-action GitHub Action to security scan your Kubernetes cluster configuration.
Participation in the Helm community is governed by the Code of Conduct.