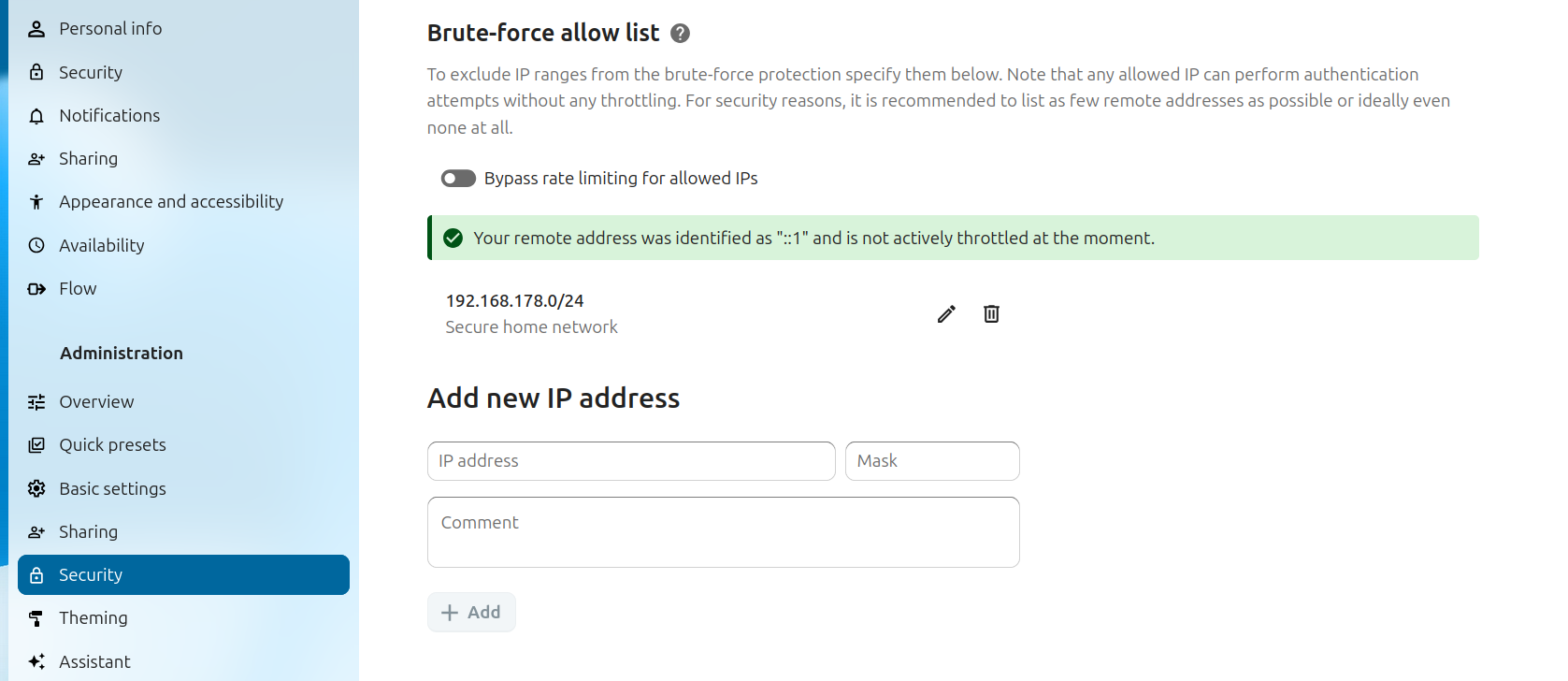
This app makes it possible (via the Web UI) to view the status of a connection and modify certain parameters of the brute force protection built into Nextcloud Server.
Currently an admin can view the status of the IP address they are connecting from as well as specify IPv4 or IPv6 addresses and ranges to exempt from brute force protection.
Additional enhancements may be made in the future, within this app and/or in combination with Nextcloud Server for additional monitoring or behavior adjustments related to brute force protection.
Tip
Most nuisance triggering of brute force protection can be resolved through proper configuration of reverse proxies. In other cases, select IP addresses that need to be whitelisted can be configured within this app (while leaving brute force protection enabled). This can be useful for testing purposes or when there are a lot of people (or devices) connecting from a known, single IP address.
Important
Disabling this app merely removes your ability to adjust brute force related settings - it does not disable brute force protection in Nextcloud Server itself. If that is your goal, you must set a special value in your Nextcloud config.php to disable brute force protection.
Brute force protection is meant to protect Nextcloud servers from attempts to guess passwords and tokens in various ways. Besides the obvious "let's try a big list of commonly used passwords" attack, it also makes it harder to use slightly more sophisticated attacks via the reset password form or trying to find app password tokens.
If triggered, brute force protection makes requests - coming from an IP on a brute force protected controller - slower for up to a 24 hour period
The app is shipped and comes with the installation of Nextcloud Server. No additional steps are necessary to install.
Old versions of this remain available through the app store. They can be installed through Nextcloud's app management UI.
Note
Newer versions of the app are not included in the app store since it is now a shipped app.
As a shipped app:
- changes are posted within the Nextcloud Server changelog.
- releases are not posted in this GitHub repository, but they are tagged for code perusal.
- it is automatically kept up-to-date with each Nextcloud Server release.
- The user interface added by this app is found under Administration settings -> Security under the Brute-force IP whitelist heading.
This application merely manages some of the settings associated with brute force protection. To understand how that protection works, review the How it works section of Brute Porce Protection chapter in the Administration Manual.
- The functionality of Brute Force Protection itself is documented in the Nextcloud Administration Manual in the Brute force protection chapter.
- Additional special configuration parameters are also documented in the Nextcloud Administration Manual in the Configuration Parameters section.
- There are also several brute force related
occcommands.
- Developers can enable brute force protection on security sensitive areas of their application as described in the brute force protection section of the Developer Manual.
- The optional
suspicious_loginapp. - Using
fail2banwith Nextcloud Server. - The Hardening and security guidance chapter of the Nextcloud Administration Manual.
- The Logging chapter of the Nextcloud Administration Manual.
- The optional audit log provided by the
admin_auditapp. - The Reverse Proxy configuration chapter of the Nextcloud Administration Manual.
- Rate limiting in Nextcloud Server (built into some sensitive areas) and using it
- Bug reports: https://github.com/nextcloud/bruteforcesettings/issues (not for general troubleshooting assistance)
- Enhancement ideas: https://github.com/nextcloud/bruteforcesettings/issues
- Pull requests: https://github.com/nextcloud/bruteforcesettings/pulls
- Troubleshooting assistance: https://help.nextcloud.com
- Code: https://github.com/nextcloud/bruteforcesettings/tree/master
Keep in mind that the brute force protection implementation is primarily within Nextcloud Server itself so for some details it may be more appropriate to look there.